
Unauthorized access to confidential company data end systems can occur in the cloud due to weak security measures, poor configurations, or lack of MFA.
The most immediate impact of a ransomware attack is the financial cost. This includes the ransom demanded by cybercriminals, potential loss of revenue due to disruption in operations, and expenses related to recovery efforts.
Granting cloud access permissions often disregard the principles of least privilege, resulting in excessive authority and increased risk regarding the sovereignty and potential destruction of data.
If an attack leads to a data breach involving customers’ personal data, businesses could face hefty regulatory fines, especially under laws like GDPR.
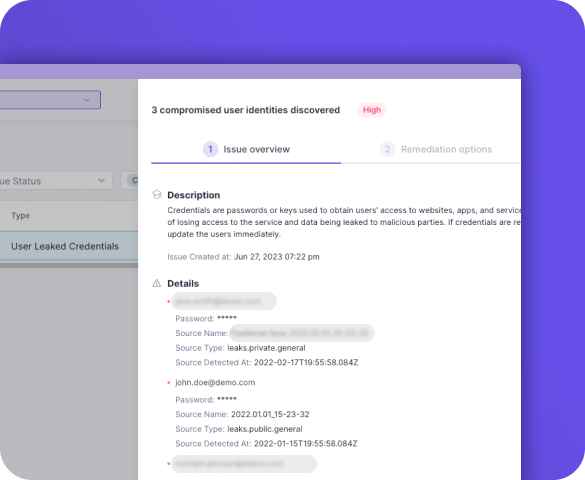
Guardz continuously monitors the dark web for leaked credentials and signs of exfiltrated data, which could lead to a targeted BEC attack.
Employees are the first line of defense, so training them to recognize and detect indicators of data theft fosters a culture of caution and vigilance while developing best practices around data security.
Cybercriminals frequently use sophisticated targeted attacks such as spear phishing and social engineering to trick their victims into granting access to sensitive data. Email security is one of the most robust defenses to block these attempts.
Guardz scans customer cloud environments for digital assets with excessive sharing permissions and abnormal activity.

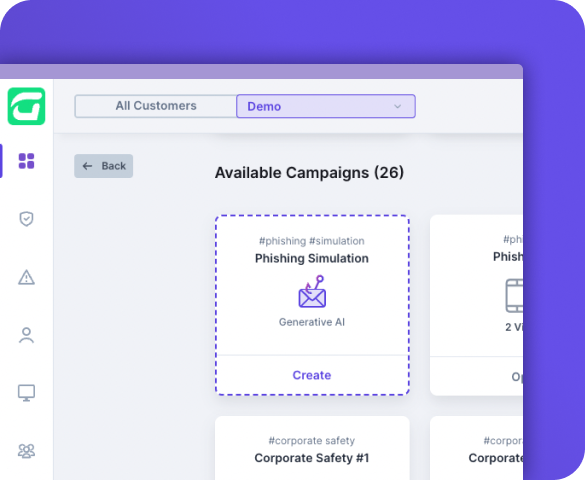
Guardz ensures up-to-date employee training by notifying admins of training status and recommending industry-standard best practices. Customizable campaign planning allows businesses to target specific users and meet company goals.
Phishing simulations help employees learn to avoid threats related to data loss, while mandatory evaluations measure the impact of training.
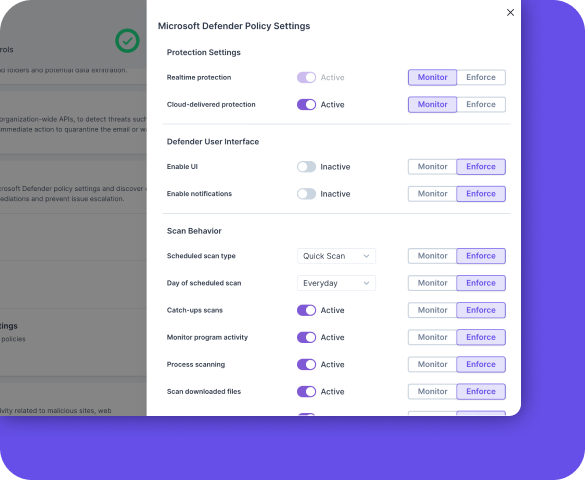
The Guardz Endpoint Protection provides an instrumental layer of security by pairing it with Microsoft Defender Antivirus to manage endpoint security for your organization proactively. Performing ongoing scans in real-time on each device, the solution uncovers potential gaps in security posture, alignment with Defender policy settings, and detection of real-world threats.
Strengthening internal security, Guardz assures your organization’s digital assets are protected against targeted digital attacks that exploit internal weaknesses. Guardz identifies these threats and provides real-time responses, including automated remediations, generating playbooks to address any issues, and offering a valuable snapshot of all processes for thorough investigation and research.
Guardz continuously the dark web to identify leaked credentials that may lead to the risk of account compromise. Bad actors frequently begin their attack chain by acquiring stolen user names and passwords that give them access to private repositories.
Guardz ensures that employees’ and clients’ digital assets remain secure from targeted attacks by cybercriminals for financial gain or other malicious purposes.
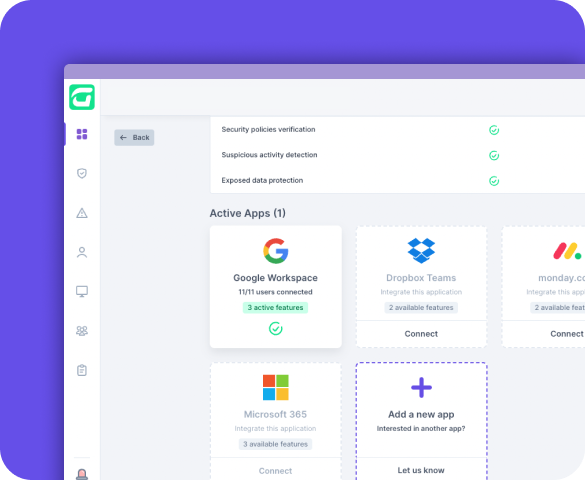
Guardz ensures cloud data protection by seamlessly linking to customer applications and meticulously scanning files and folders for excessive sharing permissions. Identification of external shares outside the domain, or public links, is promptly reported for the admin’s review.
Guardz examines all digital assets within the customer cloud environment. Files and folders presenting a potential risk are flagged for immediate attention. IT administrators have the autonomy to revise access permissions and safeguard data integrity.
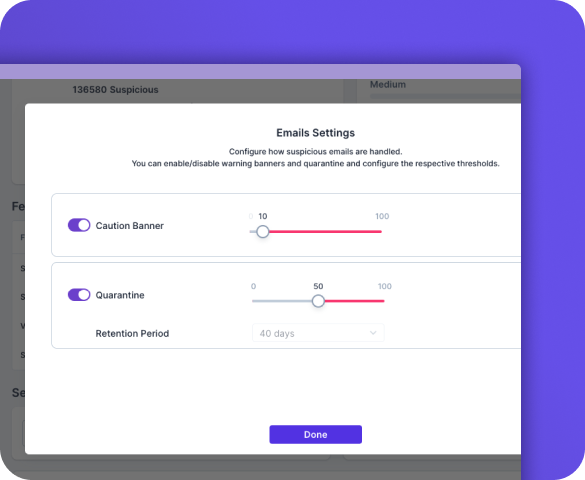
Guardz streamlines email protection with its fully managed, cloud-based solution that eliminates manual setup and seamlessly integrates with Microsoft 365 and Google Workspace accounts. Leveraging advanced predictive analysis, global intelligence tools, and continuous updates, Guardz provides robust defense against multiple attack vectors.
High-risk emails are immediately placed into quarantine to programmatically remove the threat. Employees receive warnings and recommended actions for potentially harmful emails, while IT admins can automatically flag and remove malicious messages.





Data loss prevention solutions work by identifying sensitive data and applying policies to control how the data is used or transferred. When a breach is identified, the system can automatically enforce corrective actions, such as encrypting data, alerting users/admins, or preventing data from being sent.
Yes, data loss prevention can provide protection against both external threats like hacking attacks and internal threats such as employees inadvertently or deliberately leaking data.
A data loss prevention system can help your organization prevent accidental or intentional data leaks. This includes vital customer information or company proprietary data. DLP offers your security team full insight into data movement, guarding data in transit or at rest on devices. Using DLP ensures protection against data leaks, helping you avoid operational issues, compliance breaches, potential penalties, and damage to your reputation.
Yes, many DLP solutions have the capability to control and restrict the copying of sensitive data onto external storage devices.
When choosing a DLP solution, consider factors like your company’s size, the nature of the data you handle, regulatory requirements, cost, ease of use, and its compatibility with your existing IT infrastructure.
Demonstrate the value you bring to the table as an MSP and gain visibility into your existing or potential clients’ external postures.
This guide provides you with innovative strategies and expert insights to elevate your MSP business, strengthen client trust, and stay ahead of ever-evolving threats.

Demonstrate the value you bring to the table as an MSP and gain visibility into your existing or potential clients’ external postures.
This guide provides you with innovative strategies and expert insights to elevate your MSP business, strengthen client trust, and stay ahead of ever-evolving threats.