We are excited to share our latest product updates designed to empower our MSP partners and bolster your cybersecurity capabilities. Our newly introduced features and improvements are crafted to streamline your processes, boost client engagement, and drive growth.
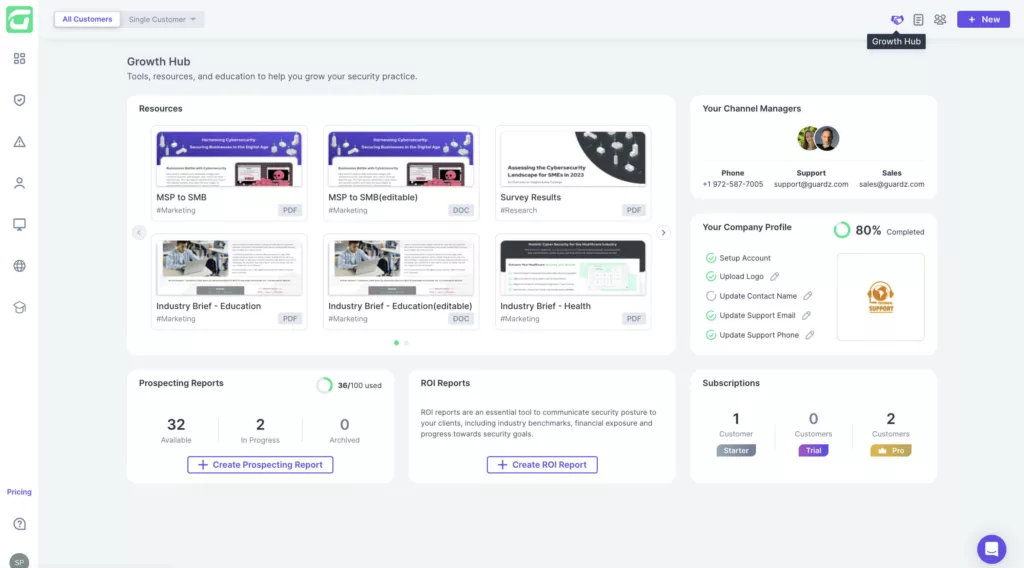
Growth Hub
We are thrilled to introduce our Partner Growth Hub – a dedicated experience empowering our MSP partners. By centralizing crucial tools and resources, we aim to streamline your processes, enhance client engagement, and ultimately drive your business growth. The narratives driven through this content not only showcase the value of Guardz but also position you as a trusted advisor in the eyes of your clients.
Offering a vast array of features tailored to meet your unique needs, our Partner Growth Hub is more than just a feature, it’s a testament to our dedication to your success. Explore this feature-packed hub and let us help you push the boundaries of your business today!
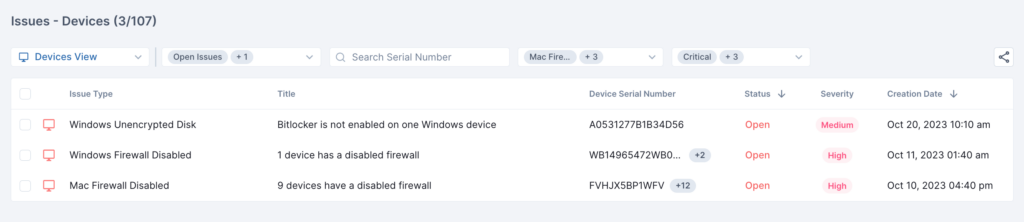
Device Encryption & Firewall
The Guardz endpoint agent has been updated to further strengthen device posture monitoring. It now actively scans user devices to verify disk encryption and assess the health of firewall settings. This enhancement complements our existing capabilities, which include identifying gaps in security settings related to the OS and AV tools.
Integrating closely with Windows (Defender Firewall & Bitlocker) and MacOS (Mac Firewall & FileVault), when the agent detects any discrepancies or vulnerabilities, it will promptly generate an issue with an actionable playbook. This provides administrators and users with clear, step-by-step guidance to manually remediate and ensures optimal device security.
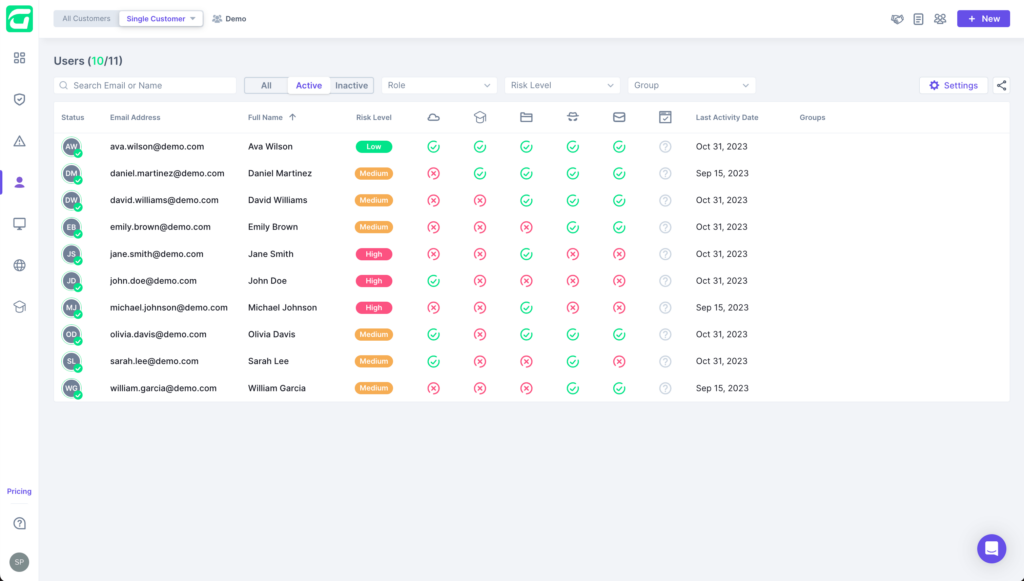
Enhanced User Page
Our focus has always been on the user, and by strengthening this commitment, we bring you an enhanced User Page. The revamped page is designed to aggregate risk associated with individual users and their issues across the Guardz platform. The new setup offers a transparent view of users and their relevant security controls, highlighting which are problematic and secure and giving a comprehensive idea of each user’s risk status. Comprehensive user details and metadata are just one click away in the details drawer.
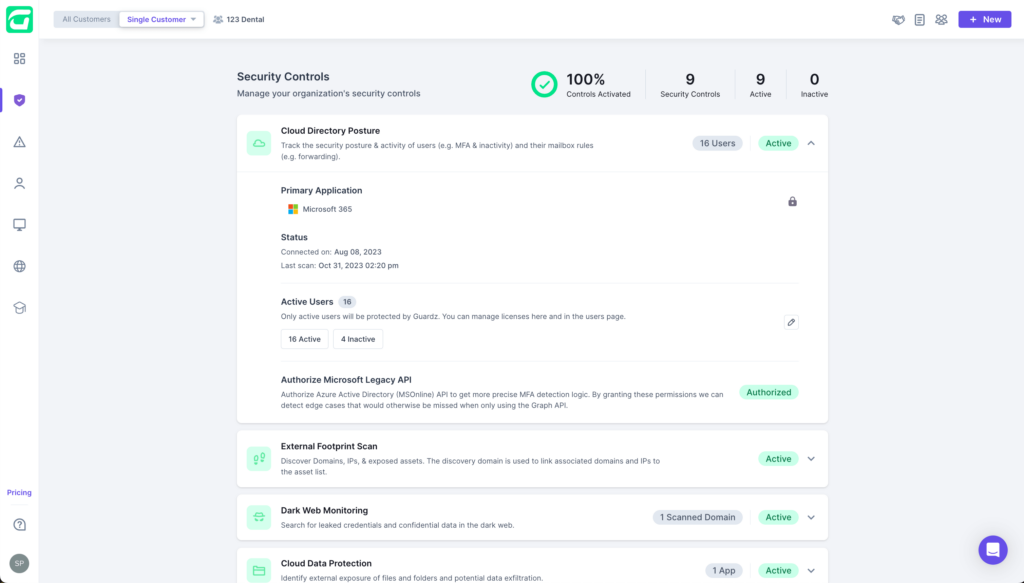
Legacy MFA
We realize that multi-factor authentication at Microsoft can be complex. That’s why we have introduced a new authorization step (MSOnline API) for more accurate MFA detection logic as protocols transition to “legacy” status. This added feature is available at your convenience under Security Controls > Cloud Directory Posture > Authorize Microsoft Legacy API.
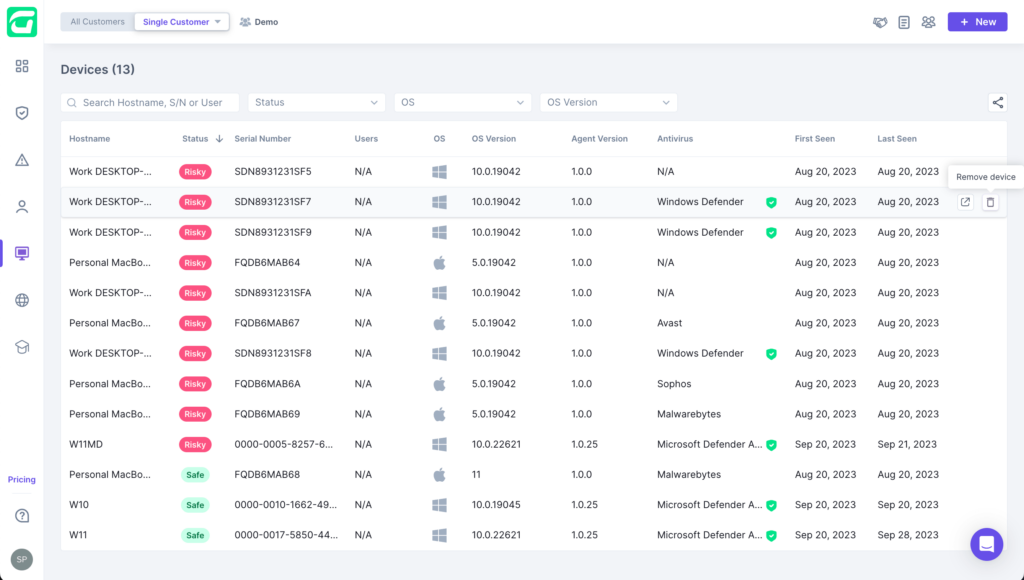
Delete Device from List
Simply access this feature by clicking on the trash icon found in the right column of the device table. Keep in mind that while the device is removed from the list, it reappears if it sends another heartbeat.
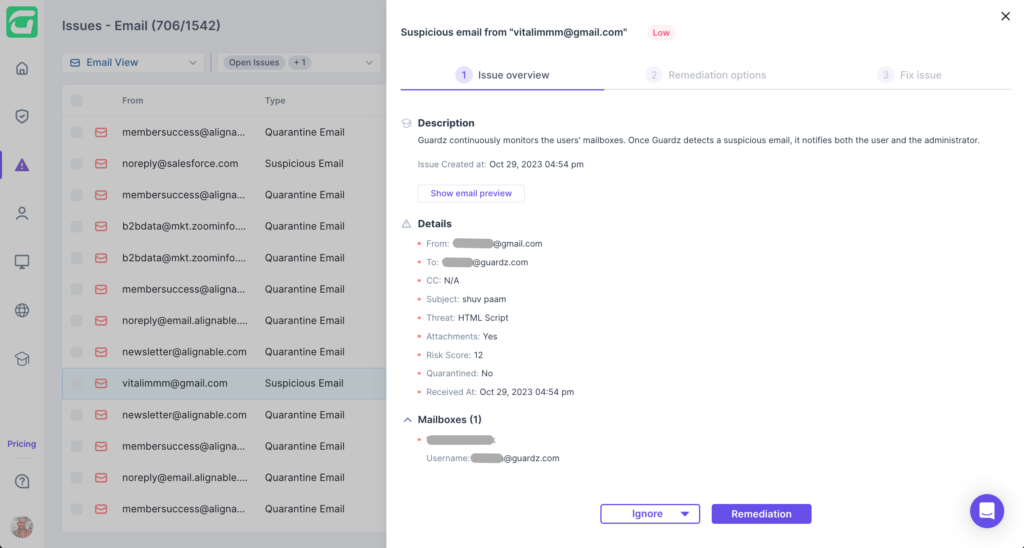
Email Script Scanning
Raising the bar in email security, we present our latest feature – Script Scanning. This email security tool effectively detects hidden HTML scripts in email attachments that could pose a potential threat. Our advanced algorithms scan for and identify risks, offering an added layer of protection against phishing and malware. It runs quietly in the background, injecting warning banners for risky content or quarantining emails to keep your inbox safe.
Keep your eyes peeled for some other exciting releases, including a new search & filter design to help you focus on essential data, important updates to the billing page to simplify subscription management, a brand new Security Posture report to show your customers the ROI on the work you do, and early ransomware detection & response capabilities on the endpoint.
We hope you enjoy the new updates!
- Share On: